Data Management for your JD Edwards Data
Is your organization thinking about the subject of data retention for your JD Edwards system? In this article we explore key discussion points around developing a meaningful Data Retention Policy.
Read more >
What is Data Archiving?
Find out how Data Archiving and Data Purging fit into Data Lifecycle Management
Read more >
How to delete JD Edwards data that has passed its retention date and not just archive it
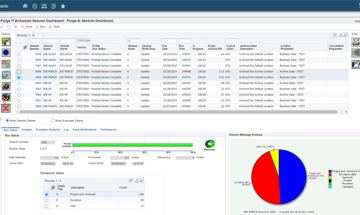
If your data archive is growing and you need to take action, check out how functionality in Purge-it Version 5.2 allows the possibility to completely remove old data from the archive
Read more >
How to measure the success of Data Archiving (Part 3)
In the final part of this 3 part series of blog articles 'measuring the success of data archiving', we look at two more customer examples
Read more >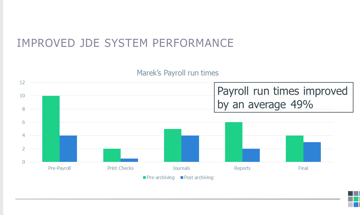
How to measure the success of Data Archiving (Part 2)
In part 2 of 'measuring the success of data archiving', we look at real customer examples
Read more >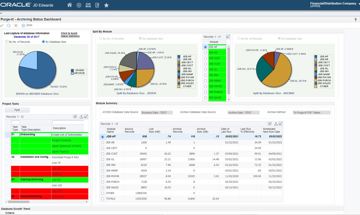
How to measure the success of Data Archiving (Part 1)
Can you measure the impact of data archiving? How do you demonstrate ROI? We address these questions and others in this JD Edwards article
Read more >
What is Oracle Validated Integration (OVI)?
Find out how Klik IT achieving Oracle Validated Integration with JD Edwards EnterpriseOne Expertise for its integration of Purge-it can help you and your organization
Read more >
Purge-it Version 5.2 FAQs
Explore some of the most frequently asked questions relating to the latest release of the JD Edwards data archiving solution, Purge-it
Read more >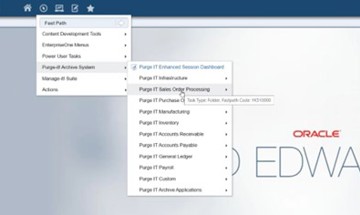
Is Purge-it easy to use for E1 data archiving?
Purge-it customers tell us one of the key drivers for choosing the data archiving solution is its usability. In this blog post we look at the main factors that make Purge-it easy to use.
Read more >
What is Purge-it?
Find out all about Purge-it. How it works, who it's for and what it offers JD Edwards users
Read more >Get a JD Edwards data healthcheck
In this blog post we look at how the JD Edwards data archiving solution Purge-it! gives your JD Edwards system a health check.
Read more >
30 features of Data Archiving with Purge-it
Discover the top 30 features of data archiving with Purge-it that make it a truly easy product to implement.
Read more >
What is JD Edwards Archiving as a Service?
You're no doubt familiar with the as a Service model. Discover the business benefits of opting for Archiving as a Service for your JD Edwards E1 data archiving needs in this blog post.
Read more >
8 reasons to automate your JD Edwards archiving
Checkout this second blog post on archive automation. We zoom in on the 8 top reasons to automate your JD Edwards archiving.
Read more >
What is archive automation for JD Edwards?
Find out how human intervention in the routine task of archiving JD Edwards data can be greatly reduced. We’re talking about archive automation. It can help achieve remarkable ongoing efficiencies.
Read more >What is meant by an integrated JD Edwards archiving solution?
What's the difference between an external and an internal archiving product when it comes to JD Edwards archiving? Read our short blog post as we summarize the differences.
Read more >
Deteriorating system performance negatively impacts many job functions across an organization. Find out why you system is slow. Discover how to speed up your JD Edwards system and enhance the user experience.
Read more >
Find out which version of Purge-it! your organization is running
Make sure your organization is maximizing its use of the archiving solution Purge-it! Find out which software version you have. Discover the latest product enhancements and new Purge-it! features and functionality.
Read more >
How Klik IT started 25 years ago...and what's next?
As Klik IT celebrates 25 years in business in 2023, we took some time out to chat to CEO, Terry Clarke.
Read more >
Find a JD Edwards archiving solution that works for your business. Ask these 5 questions.
Is your organization looking for a 3rd party archiving solution?
Checkout 5 key questions to ask when evaluating JD Edwards archiving tools and solutions.
Read more >
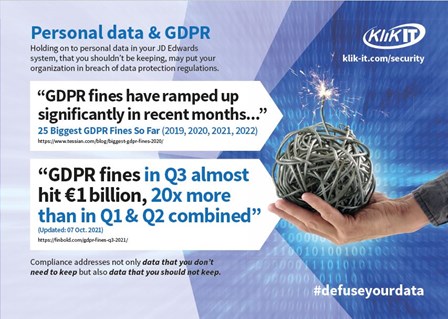
Data Retention & Security
Data Retention and Security is a hot topic and a vast subject.
In this Blog post we look at Data Retention and Security from the perspective of organizations running JD Edwards. We cover the key considerations as we see them and provide links to industry articles and information for a broader view of the subject.
Read more >Data Retention & Security
JD Edwards Data Security
Is your organization sitting on a ticking time bomb?
Data retention and security is a hot topic and a vast subject. The impact of a security breach or a cyber-attack can be far-reaching. Fines and/or compensation claims are affected by the amount of data, and the number of data items stolen. Repercussions for a business can be devastating. There is also the untold damage to a company’s brand.
In this Blog post we look at data retention and security from the perspective of organizations running JD Edwards. We cover some key considerations, but also provide links to industry articles and information for a broader view of the subject.
Has your JD Edwards ERP system experienced exponential data growth over many years?
Factors that can lead to an accumulation of large volumes of data
- Natural business growth
- Implementation of new features and modules within JD Edwards
- Acquisition of new companies
- Rolling out the JD Edwards implementation over time
- Introduction of new technologies
As the quantity of data continues to grow, the risk of data or security breaches is ever more present.
What risks are buried in this huge amount of JD Edwards data?
Holding onto vast quantities of data in your Production environment could dramatically increase the consequences of a security or data breach.
How to minimize your risk
If data is not useful to you operationally, or required to be held legally, then you should consider completely removing that data. In so doing, the company’s data footprint is reduced as are the consequences of a security breach and possible resulting legal liabilities.
Legal Compliance and Liability
With data comes a legal responsibility to manage and protect it.
The more data you have the greater the time and cost to ensure it is correct and protected and the greater the exposure to legal liability and potential litigation (with its associated costs).
How do you know which data to hold onto?
Legal retention periods tend to be industry and country specific.
Legal acts and in some cases supplier and or customer contracts determine how long data must be kept. Retention of too much or too little data can result in serious implications for an organization.
Local and national governments (and other organizations) can have specific clauses in their contractual agreements, detailing what documents and data should be stored, and how long for. This gives a clear instruction that if you are dealing with these organizations, a definite amount of data should be available, if requested. That data does not have to be in a live environment, or even an on-line environment, but it should be reasonably accessible.
The process of establishing a Data Retention Policy for your organization will involve addressing compliance with statutory obligations not only for the retention but also for the disposal of data.
Optimizing Disaster Recovery
Another factor to consider is that having a smaller JD Edwards database could get you back up and running quicker; a smaller enterprise database will be restored faster.
Running a lean JD Edwards system will help your business be more agile. An agile business is better able to respond and recover from external attacks.
What is a Data Retention Policy (DRP)?
A structured and effective Data Retention Policy will define what legally needs to be kept by an organization. It will clarify the who, what, where, when, why and how of archiving and purging. The DRP should also provide a structured management framework for Information Life-Cycle Management (ILM).
Four main purposes of a Data Retention Policy
- Assure maintenance of the records and information that an organization must keep to meet operational or regulatory requirements
- Ensure timely and efficient disposal of records and information that are not needed or should not be maintained
- Minimize the amount of data to be maintained by the IT department
- Optimize the processing speed of the source system for the business users
Three core elements covered by a Data Retention Policy document
- A formal written policy statement
- A records / information retention schedule
- Procedures for executing and enforcing the policy and schedule
Why invest time in developing a Data Retention Policy for your organization?
This may not be considered the highest priority project in your organization or the most dynamic task. However, when you stop to consider the potential risk and damage to your organization and its brand of a data breach, it soon becomes clear why you should develop an effective policy for the retention and disposal of your JD Edwards data.
Case Studies
Four customers have shared their experiences of managing large volumes of JD Edwards data and talk about developing Data Retention Policies for their organizations.
What’s the cost of a data breach?
Your fine, or compensation claim will be affected by the amount of data, and the number of data items stolen.
Data Breach Costs: Calculating the Losses for Security and IT Pros
“A recent IBM and Ponemon Institute study looked at nearly 525 organizations in 17 countries and regions that sustained a breach last year, and found that the average cost of a data breach in 2020 stood at $3.86 million…”
“The report also found that the United States continued to experience the highest data breach costs, averaging $8.64 million per event.”
https://insights.dice.com/2021/02/11/data-breach-costs-calculating-the-losses-for-security-and-it-pros/
In summary
Data retention and security is about managing risks. Minimizing aspects of risk can allow you to get on with the important matter of running your day-to-day business. Two major risks that your organization can minimize by archiving your JD Edwards system are:
- Legal liabilities of data that you no longer need or must keep
- The time to get your business up and running again, in a Disaster recovery scenario.
Industry articles and information on Data Retention and Security
News Snapshot...
3 common myths around ERP data security
- Data Security is an IT problem!
Incorrect.
Data Retention and Security is the responsibility of the whole business. - We don’t need a Data Retention Policy!
A meaningful Data Retention Policy is a crucial step in proactively managing the data growth in a JD Edwards ERP system.
- JD Edwards archiving will be a complicated, drawn-out experience!
Not at all.
It’s about finding the solution that best suits your business needs. *⇓
An Introduction...to Data Retention & Security